This blog post comes as a part of broader case study about migrating server infrastructure from Windows Server 2003 and Windows Server 2008 to Windows Server 2012, including the operating systems, core network services like DNS, DHCP, but also Active Directory Services, etc. It is kind of tutorial blended with my personal review during the process.
This post particularly covers adding a Windows Server 2012 R2 domain controller in existing Windows 2003 network. It can help System Administrators in small-to-medium businesses to successfully migrate, step by step, their Active Directory Services from Windows Server 2003 to a Windows Server 2012 R2.
It is a real scenario happening in a production environment and below are the steps that were undertaken during the entire process. Screenshots are blurred on parts where the real names of the servers appear, for objective reasons. I will be using synonyms.
How this post is organized:
Part 1: Pre-checks on Windows Server 2003
- Server full backup
- Prerequisites
- Checking the health of the domain controller and domain in general
- Tools for troubleshooting Active Directory
Part 2: Pre-checks on Windows Server 2012 R2
- Setting up correct network configuration
- Patching the OS with latest Windows updates
- Initiating the wizard for adding the new domain controller
Part 3: Post-installation steps
- Changes in DHCP server
- Installing AV protection and System management software
The synonym for my Windows Server 2003 R2 name will be “server A”. The synonym for my Windows Server 2012 R2 name will be “server D”
Let’s get started.
PART 1: Pre-checks on Windows Server 2003
The Windows Server 2003 R2, or server A, is a server which holds multiple roles like: Domain Controller (Active Directory), DNS Server, DHCP Server, IAS (Internet Authentication Server or RADIUS), File Server, and Print Server. This is a typical setup in small and small-to-medium sized enterprises.
Server full backup
Recommendation: Do a full system backup before you start the procedure. If there is a disaster recovery procedure in place, even better.
Prerequisites
According to official documentation I found in Microsoft directories about Upgrading DCs to Windows Server 2012 and Understanding AD DS Functional Levels
and Understanding AD DS Functional Levels , in order to configure Windows Server 2012 Domain Controller within Windows Server 2003 network you must ensure that Domain Functional Level and Forest Functional Level are at least in Windows 2003 mode.
, in order to configure Windows Server 2012 Domain Controller within Windows Server 2003 network you must ensure that Domain Functional Level and Forest Functional Level are at least in Windows 2003 mode.
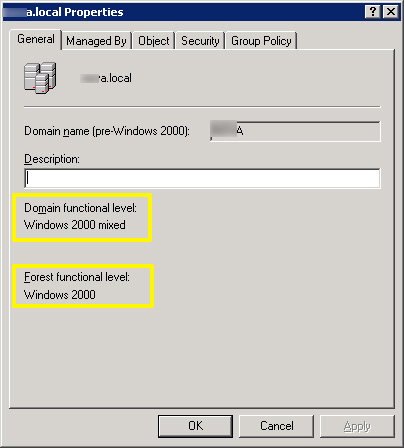
Those functional levels can be easily checked by opening Active Directory Users and Computers. Right click on the domain and choose Properties:
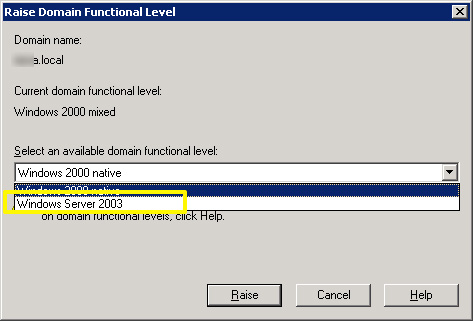
First thing would be raising the domain functional level. Using the previously opened console, right click your domain name and choose “Raise Domain Functional Level”. In Select an available domain functional level, choose Windows Server 2003 and then click the Raise button. This is one time action and it is irreversible.
In my case, this is one and only DC in the domain (no earlier generations like Windows 2000 domain or NT), so there wasn’t a reason why not to proceed.
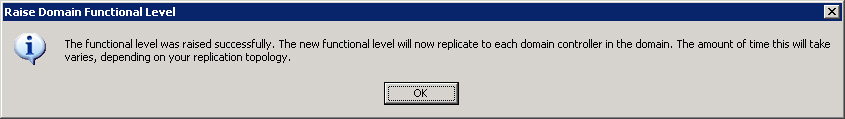
If you do this in your domain and everything goes OK you should see a confirmation message:
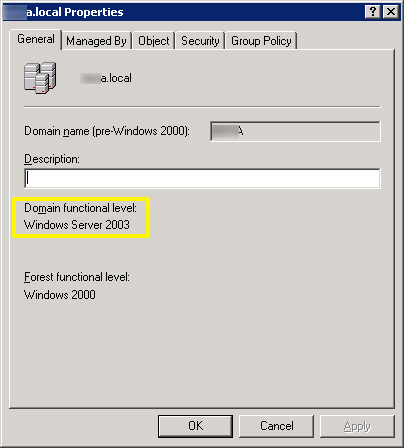
This change can be noticed if you go back in the Domain Properties:
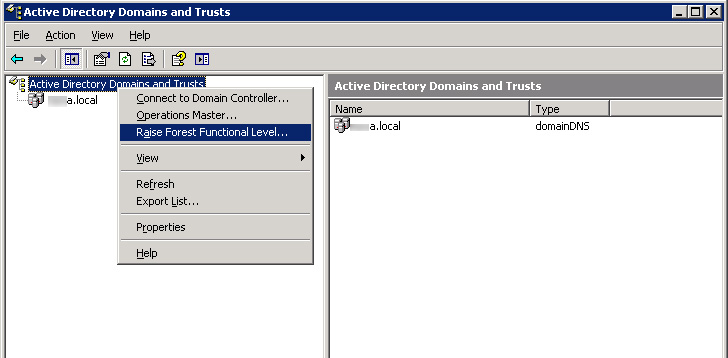
Next step is raising the Forest functional level. For this purpose, open Active Directory Domains and Trusts Console which can be found in Start menu > Administrative tools:
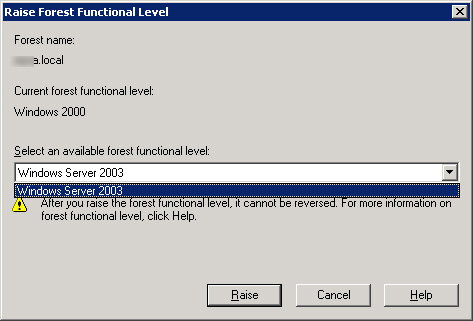
Right click the node “Active Directory Domains and Trusts” and choose “Raise Forest Functional Level…”. In the following window, from “Select an available forest functional level” choose Windows Server 2003 and then click the Raise button.
This is also one time action and it is irreversible.
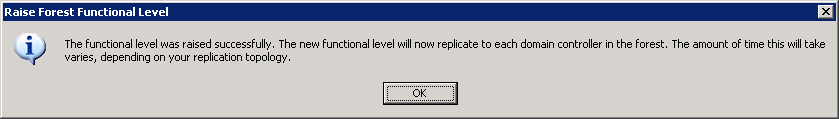
Message for successful raise followed:
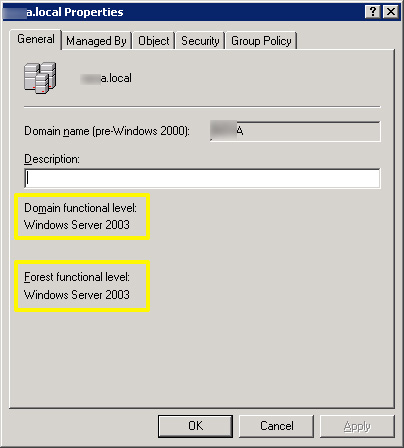
If you need to prove yourself that this operation passed successfully you can check the Properties of the domain once again:
Tip: These changes are also written in the Windows Event Viewer, specifically in Directory Service log. The Event ID for raising domain functional level is 2039 and for raising forest functional level is 2040.
Checking the health of the domain controller and domain in general
In network with multiple domain controllers next step would be to verify which DC holds each of the FSMO roles and how do they replicate between each other. Also, performing a thorough Domain Controller health-check and ensuring their availability is crucial for a successful transition.
and how do they replicate between each other. Also, performing a thorough Domain Controller health-check and ensuring their availability is crucial for a successful transition.
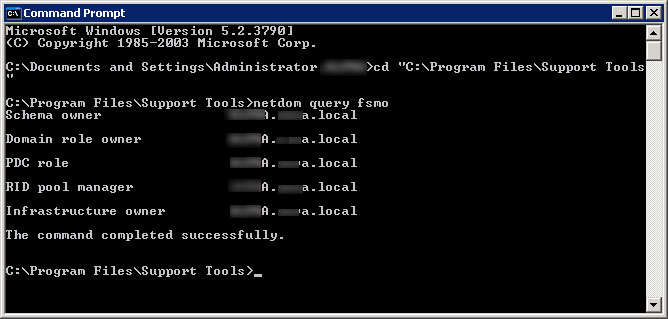
Check which DC holds FSMO roles by opening the command prompt and running the following command:
C:\Program Files\Support Tools\netdom query fsmo
Netdom is located in the Support Tools package which by default is not installed on your Windows Server 2003. You may download it from here .
.
Since in my environment there was only one DC, the result was expected and it was the Server A:
Finally the last step before Active Directory preparation for the first Windows Server 2012 R2 domain controller, is checking the health of the domain.
By executing the dcdiag command from the Support Tools, a lots of tests will be executed against your existing DC. Make sure all of them complete with a status “PASS”.
In my case I noticed certain problems with the systemlog test. After googling the errors that showed up I realized that the systemlog test reads out most recent logs from the System log in the Windows Event Viewer. I opened the Event Viewer and I saw errors related to failed user authentication in IAS (Internet Authentication Service) which wasn’t a server-side problem, but a user in my domain that was continuously typing a wrong password. Then I continued to scroll backward and didn’t notice some significant problems.
that showed up I realized that the systemlog test reads out most recent logs from the System log in the Windows Event Viewer. I opened the Event Viewer and I saw errors related to failed user authentication in IAS (Internet Authentication Service) which wasn’t a server-side problem, but a user in my domain that was continuously typing a wrong password. Then I continued to scroll backward and didn’t notice some significant problems.
Regarding this issue I found recommendations on Internet forums that you should delete the System log and start dcdiag over again, but I didn’t want to lose the events in System log because I was assured that everything is fine.
For even more detailed health check, you may consider to execute following command:
Dcdiag /e /c /v
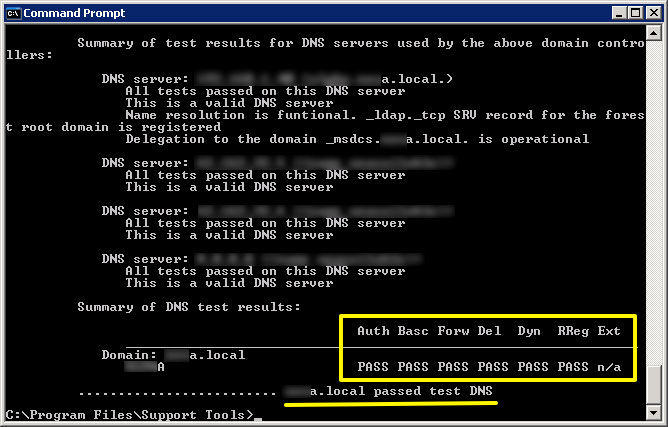
Especially after this command, make sure you see six PASSes in the result:
If you want to test only DNS, run this command:
dcdiag /test:dns
To check if DCs are replicating data correctly run the repadmin command :
:
Repadmin /showrepl /all /verbose
Tools for troubleshooting Active Directory
If you are doing these tests against your domain and some of them didn’t pass, you will have to check and fix all errors. Here are couple of useful links where to start from:
Tools for troubleshooting Active Directory
Diagnosing and troubleshooting Active Directory problems
Top 5 free Microsoft tools for Active Directory Health
Active Directory Replication Status Tool . Read the TechNet blog how this works
. Read the TechNet blog how this works .
.
My domain passed all the tests, so it was ready to accept first Windows Server 2012 R2 domain controller in Windows Server 2003 network.
Part 2: Pre-checks on Windows Server 2012 R2
Now, we will switch to the new box installed with Windows Server 2012 R2.
Patching the OS with latest Windows updates
After the initial OS installation, setting the RAID array and logical partitions – I installed most recent Windows updates and patches available at the moment.
Setting up correct network configuration
Next is setting the fixed values for IP address, subnet mask, default gateway and DNS server. If your server obtained these network settings from DHCP during the initial installation, now it is time to go to Network and Sharing Center and set fixed values for them since it is very important to properly configure Network Card settings for successful promotion of your new Windows 2012 Server as domain controller.
Pay attention to properly set up DNS on the new server. You should point your new Windows Server 2012 to one of the existing Domain Controllers with installed and configured DNS.
In my case, in the network card settings as DNS server for Server D, I set the IP address of Server A – since Server A is the only one DNS server.
Important: Ensure you login with an account that is member of Enterprise Admins group. The best is to use Enterprise Administrator account.
Initiating the wizard for adding the new domain controller
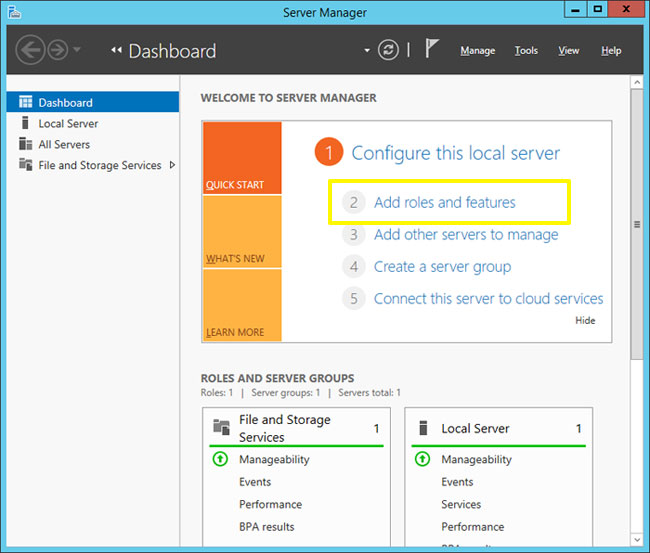
Promotion of a new domain controller starts in the new Server Manager console (dcpromo command is discontinued in Windows Server 2012).
Open the Server Manager Console and click on “Add roles and features”
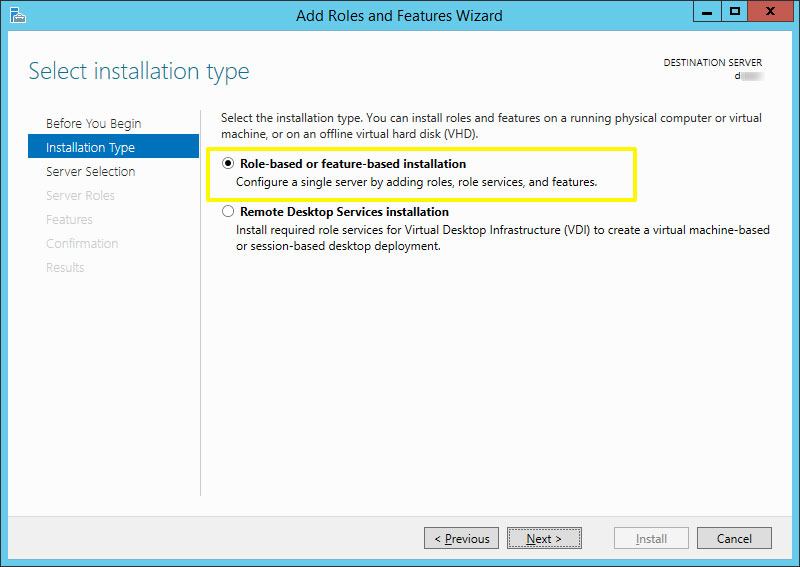
Select the option Role-based or feature-based installation
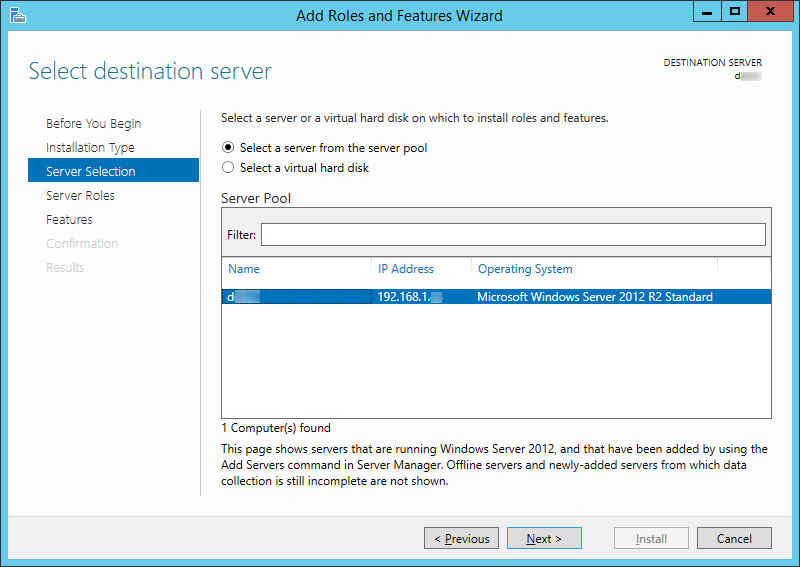
In the next window, from the Server Pool choose the server on which to install roles and features. In my case, only Server D was available:
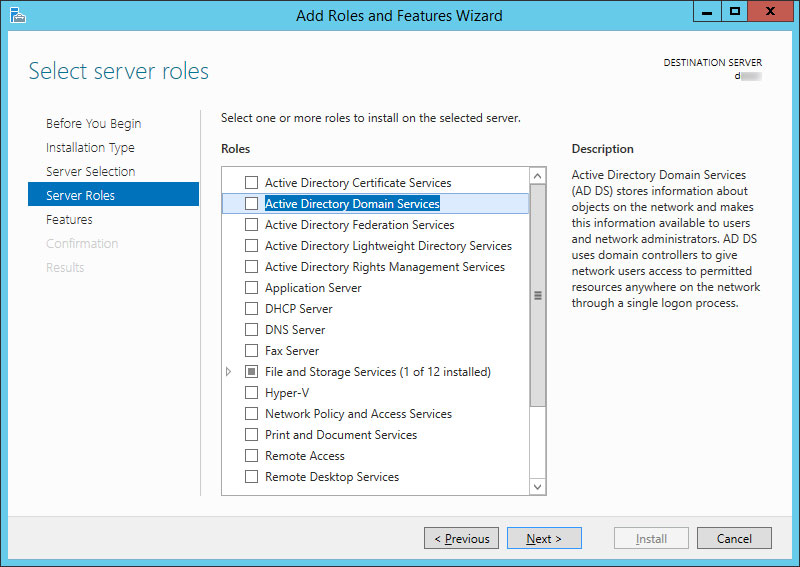
Then, select Active Directory Domain Services:
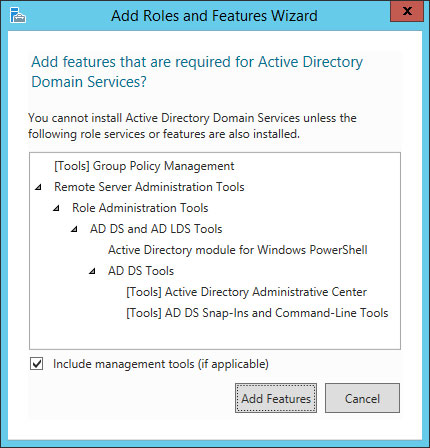
Accept the default features by clicking Add features:
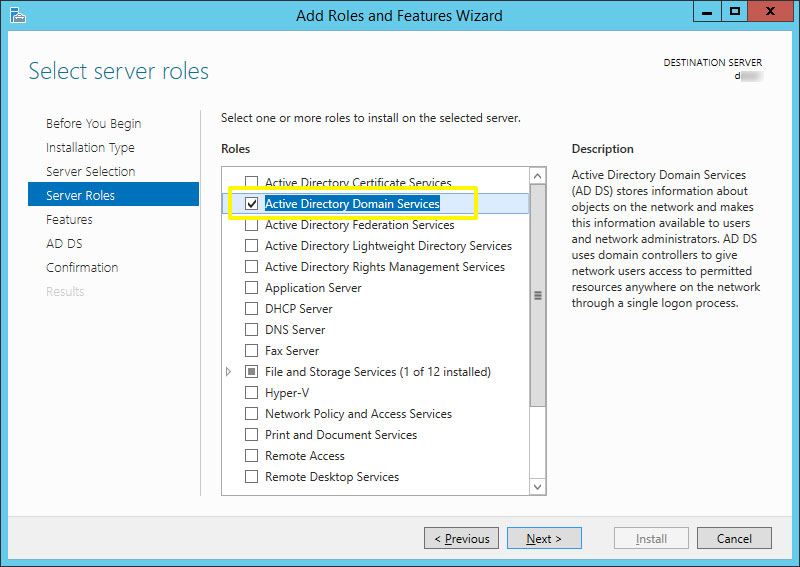
Ensure that the required role “Active Directory Domain Services” is ticked and then click Next:
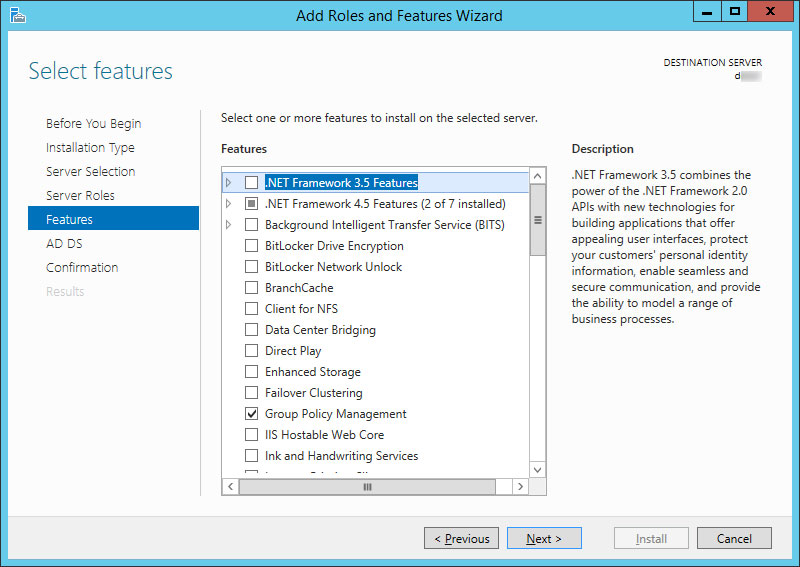
On next window “Select features” just click Next. There isn’t necessary to add additional features at this step.
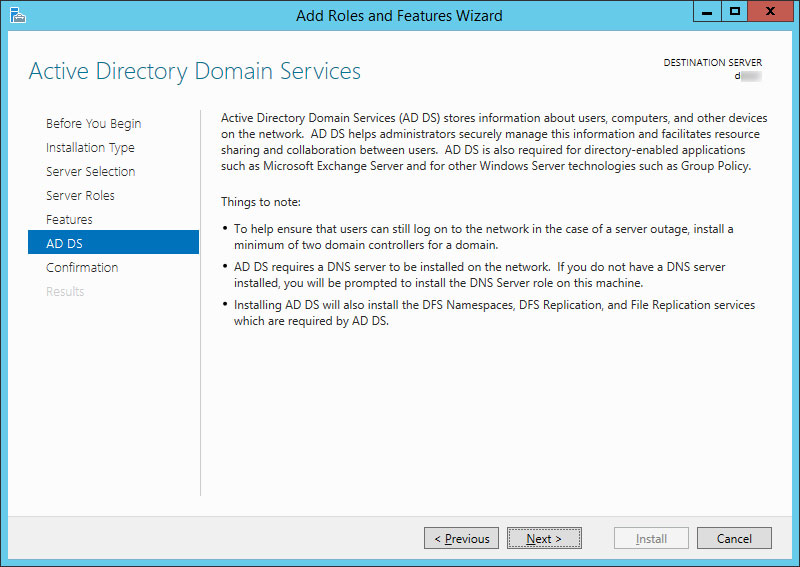
On next window read the information about Active Directory Domain Services, then click Next:
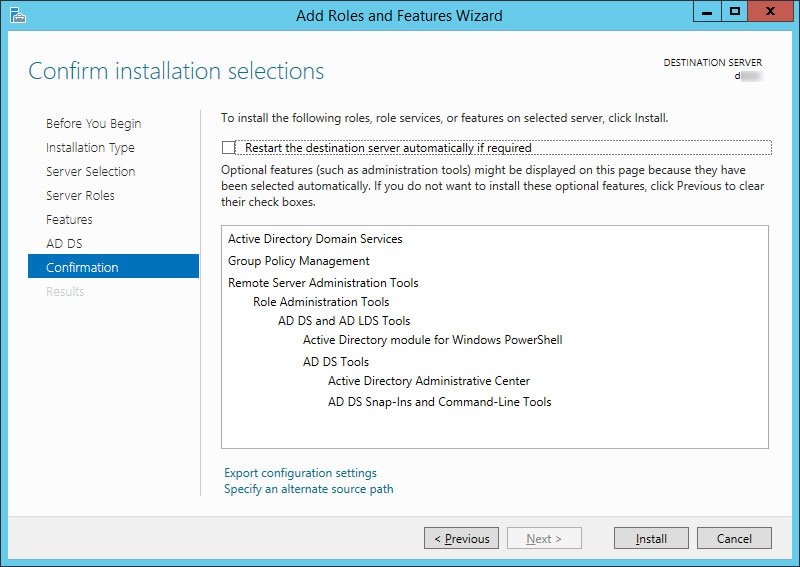
On next window “Confirm installation selections” click Install (it is not necessary to tick the option for Restart):
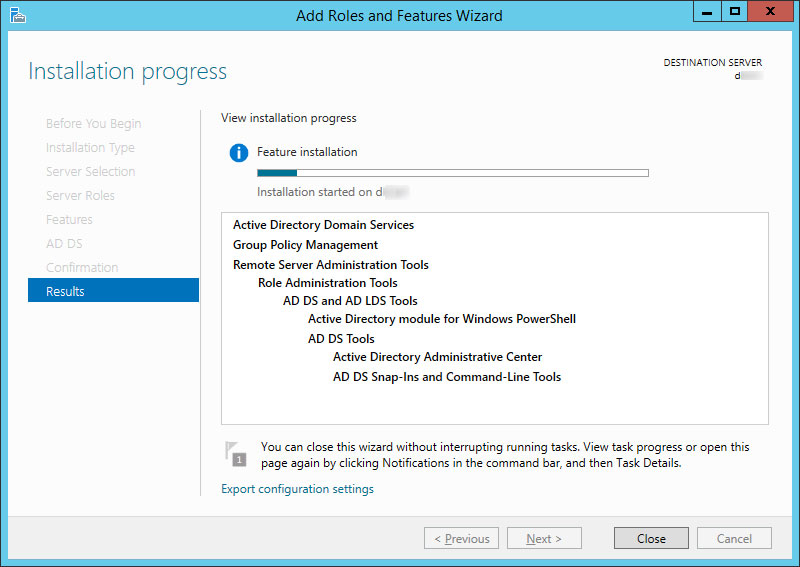
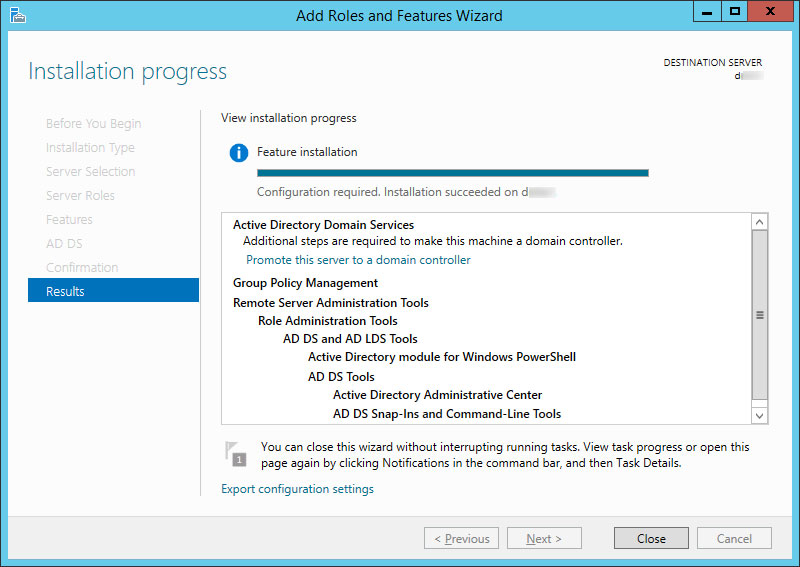
Installation has started:
The installation has completed successfully:
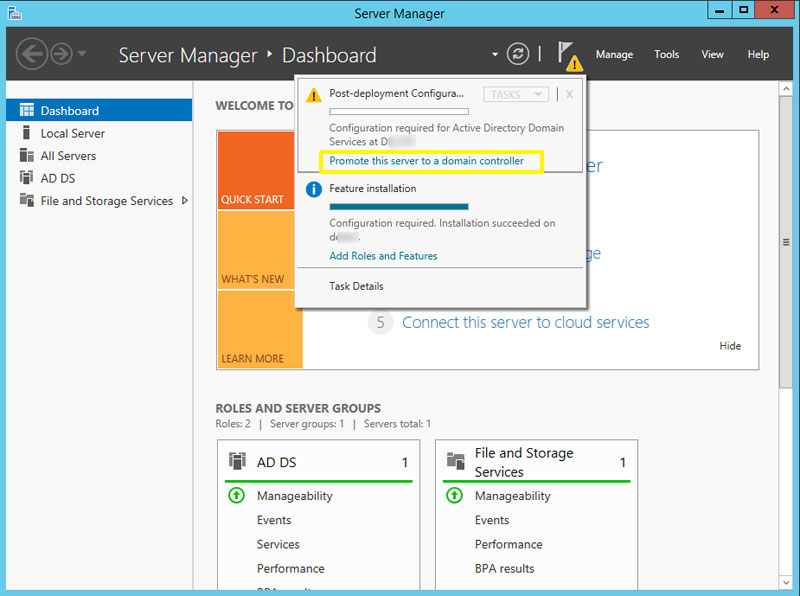
You can start DC promotion either by clicking “Promote this server to a domain controller” or by clicking Close and starting it from the Dashboard. I chose the second option.
In the header section of the Dashboard you will notice an exclamation mark which notifies that post-installation steps are required:
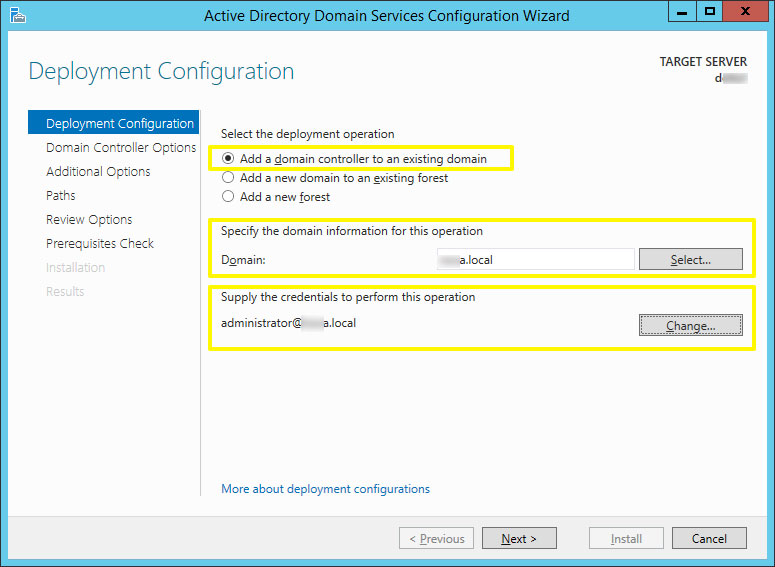
The wizards has just started and on the next window select the option Add a domain controller to an existing domain. In the “Specify the domain information for this operation” section, click Select button and choose your domain:
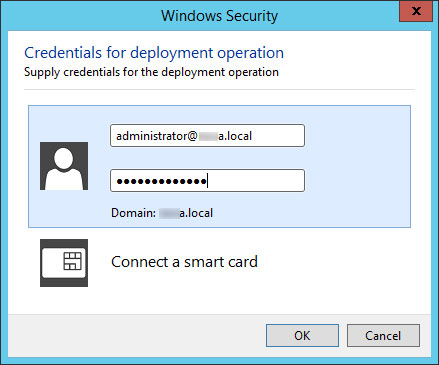
In the “Supply the credentials to perform this operation” section, click Change and make sure you provide the Enterprise Administrator credentials in the following format administrator@your_FQDN:
Click OK, then Next.
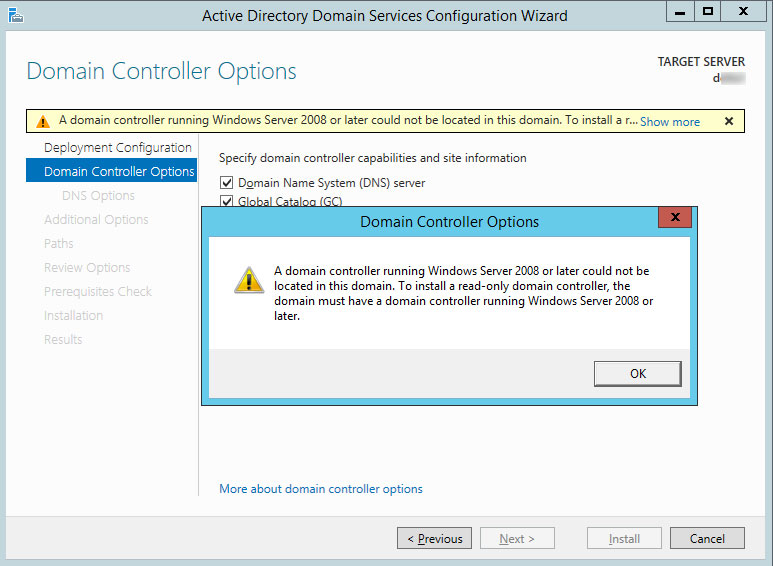
Next window was just a warning in case I would want to install a Read-Only Domain Controller (RODC). So, minimum requirement to install Windows Server 2012 R2 as RODC is to have a domain controller running Windows Server 2008 or later.
In my case, I was adding the first fully functional Windows Server 2012 domain controller in Windows 2003 network, so I just safely skipped this warning.
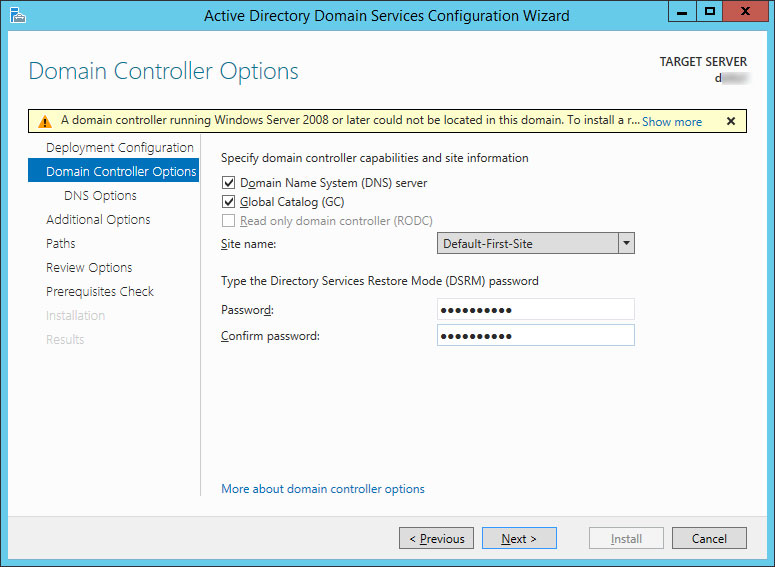
Just ensure that both options for Domain Name System (DNS) Server and Global Catalog (GC) are ticked. Then, select the Site name where this DC will belong and type the Directory Services Restore mode password:
Click Next.
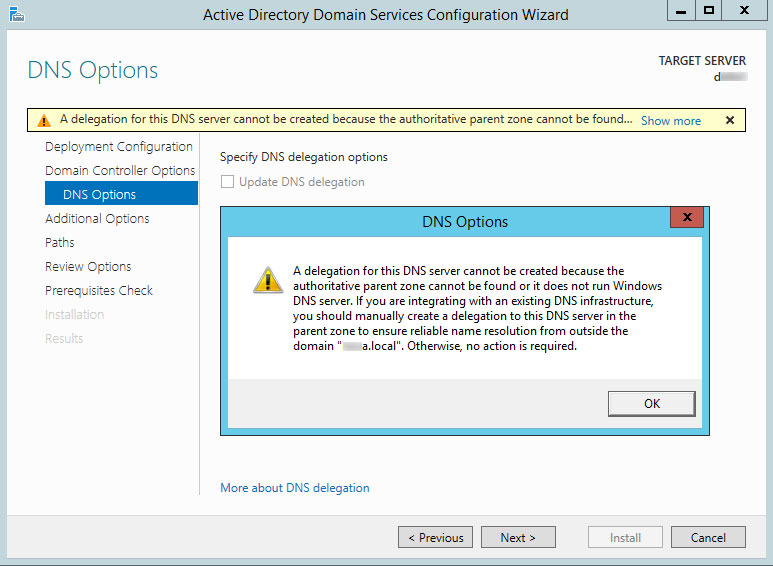
Read the warning, click OK and then Next (this server is not DNS server yet).
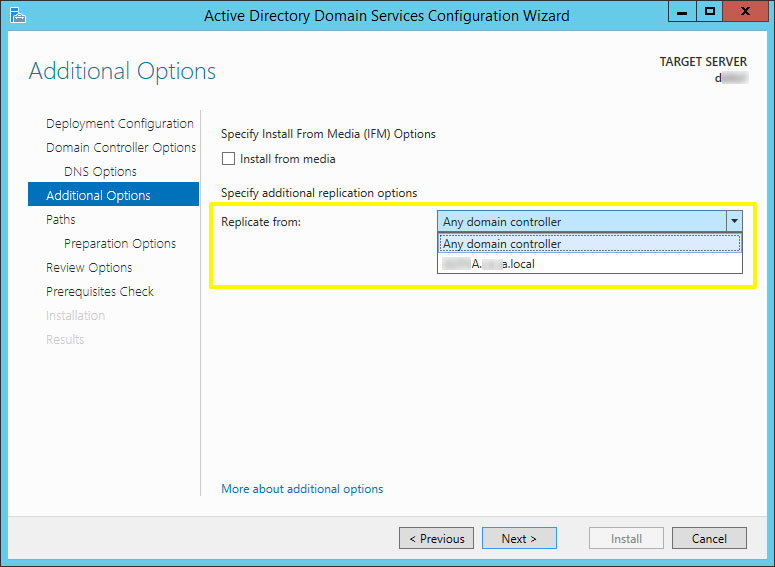
In Additional Options window, you have option to specify the location where the new DC should replicate from:
Click Next.
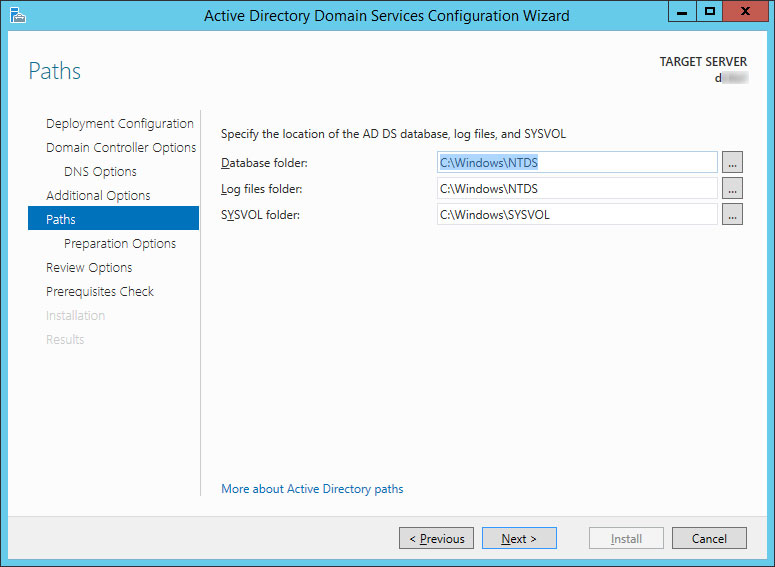
On Paths window, leave the default locations and click Next
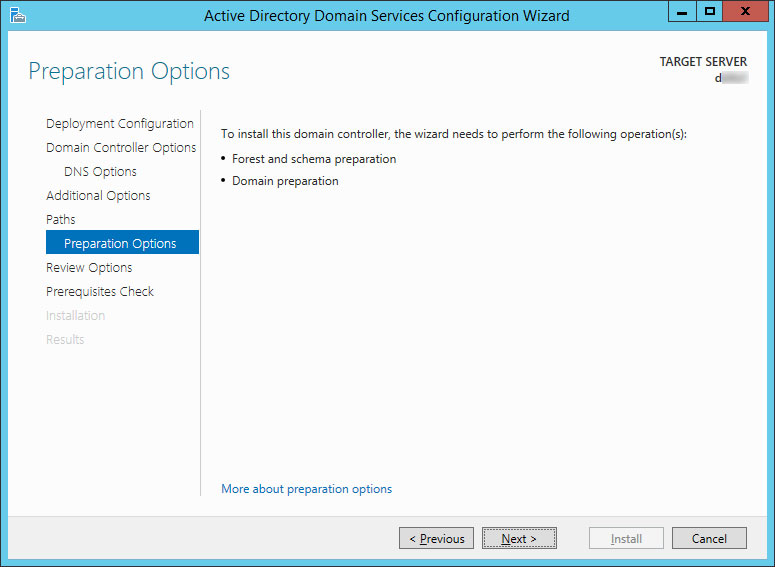
In this step the Wizard informs you that it will perform Forest/Schema and Domain preparation. Click Next.
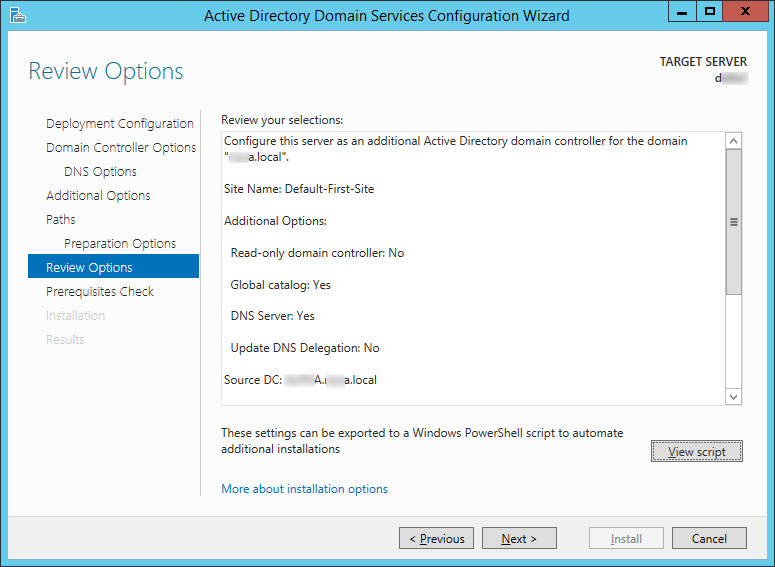
Next window is summary where you can review all the steps that will be performed
Optionally, you may click View script button to see the powershell script that will be executed in the background. Click Next.
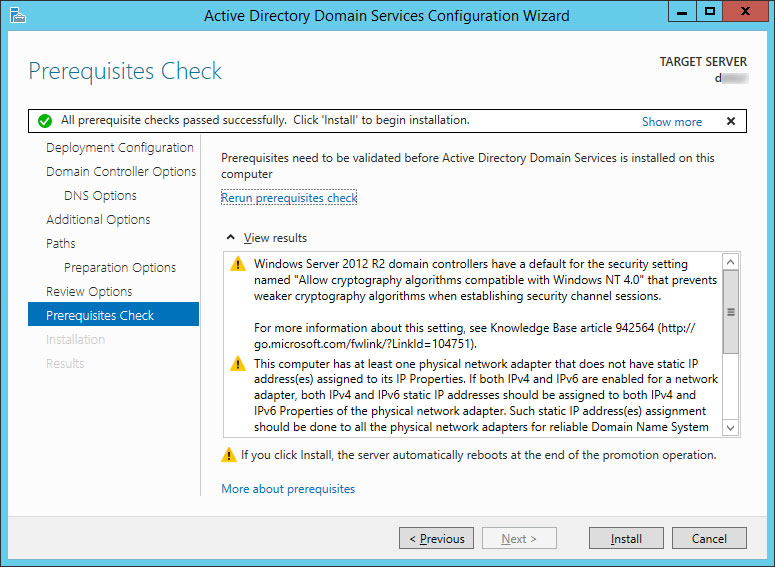
Prerequisites check starts. If everything is fine you should see a green check-mark:
Click Install. The wizard started the process of: upgrading the forest, DNS installation, configuring the local computer to host Active Directory Domain Services, Replicating the configuration directory partition, setting the computer’s DNS computer name root to match the FQDN, etc.
At the end, after the installation is over, the wizard restarts the server. It may take a while.
PART 3: Post installation steps
Changes in DHCP server
Depending on the size and complexity of your existing Active Directory it may take some time before all data is replicated. After all Active Directory objects are fully replicated to the new Windows Server 2012 R2 domain controller, as well as DNS entries – it is time to update all servers and workstations to point to this new secondary DNS server.
As for servers, you will need to do it manually.
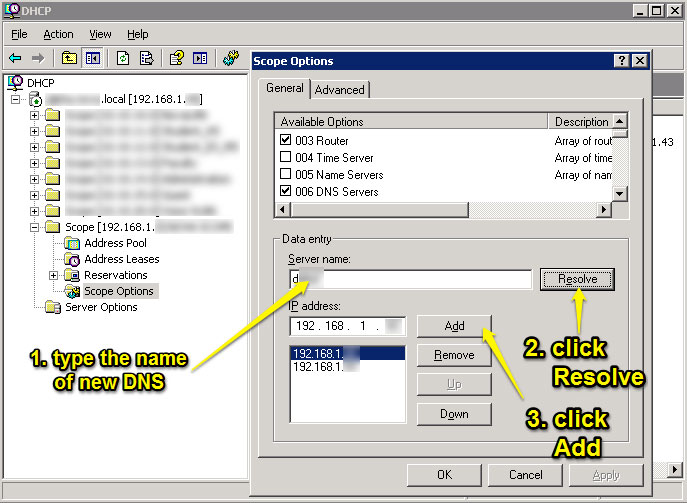
As for workstations, go to your DHCP server, open DHCP Management Console, then in each DHCP scope open Scope Options. Find option 006 DNS Servers and type the name of your new DC, then click Resolve. After the name is resolved in IP address, click Add and then OK. If you have several DHCP scopes, repeat this procedure.
Installing AV protection and System management software
After all, install appropriate security protection on the server and system management software recommended by the vendor.


This is a great primer on adding new W2K12 domain controllers. When I upgraded our domain/forest to W2K12 R2, I found some DNS entries that were not cleaned up properly, so I had to manually remove some old W2K8 R2 server entries that should have been removed from the old W2K8 R2 domain controllers; I’m not sure what happened but the due diligence paid off.
Also, you can use the W2K12 Best Practices Analyzer (BPA) to fix any issues after the domain/forest and DNS/DHCP has been upgraded, and I highly recommend using it to see where your Roles and Features are at, according to Microsoft.
Thanks Manfred!The next thing will be running the BPA. Can’t wait to see results! And regarding your experience, if I remember there were some settings about dynamic DNS updates – do you think on this? I assume you have checked these resources http://technet.microsoft.com/en-us/library/cc725703.aspx and http://technet.microsoft.com/en-us/library/cc753014.aspx. Regards
Great article. I know it’s several years (and several versions) old, but still valuable for small IT shops.
Once the new 2012 DC is running, do you then have 2 domain controllers that are duplicates of each other? In other words, if either went down would your environment still work?
Thanks in advance!
Hi Mark,
After you introduce 2012 DC, and the setup finishes successfully as explained in the article, you will have 2 DC’s running in parallel. If one goes down, as far as DNS service and user authentication is concerned – you should not have problems. But, if we talk about other services like: DHCP, network shares, etc – in this case if the DC where these services are hosted goes down then you will need to have a plan B. I hope I answered your question :)
Hi Milan,
Great artical, very helpful.
In my case I have 1 DC2003 R2 & 2 DCs 2008 R2. I am alos running Exchange 2003.
My plan is to migration to Office 365 by using Code Two (3rd oparty utility to copy mailboxes to O365).
To do so, I will need to install a new DC 2012 R2 to the environment and also a new Server 2016 to connect to AD DC Connect to Azure so that I can move forward with the Exchange migration project to O365.
Do you see any issues in my senario or the steps that I listed look good?
I would appreciate any feedback.
Zak
Hi Zak, this looks like a little more complex scenario. Honestly, it’s been a long time since I had hands-on experience with Exchange server and on the other side I don’t have experience with O365 and Code Two. I am not in a situation to acknowledge your plan, apologies.